

Explore Cisco's groundbreaking approach to enhancing security for distributed workforces without compromising user experience or impeding business operations.

A groundbreaking study highlights that the most significant value for your cybersecurity investment lies in security awareness programs.

Cyberattacks are increasing and traditional security is failing. You need ‘Zero Trust’, a holistic framework to protect your business from evolving threats. Ctelecoms can help you implement Zero Trust with identity, encryption, and cloud security. Don’t risk a breach; secure your business with Ctelecoms now.
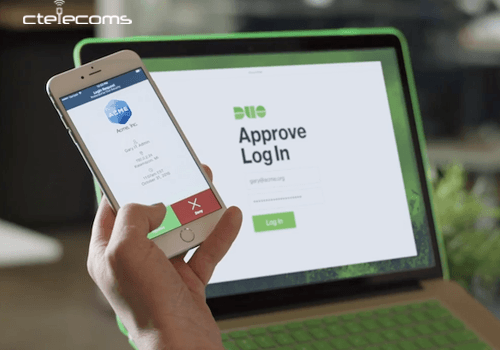
This blog explores how Cisco Duo Security and Cisco Secure Access Solution seamlessly combine to fortify the Zero Trust approach, offering a comprehensive guide for Cisco administrators and IT professionals.
Explore the core components of the Cisco Catalyst SD-WAN system, including Cisco SD-WAN Manager, Cisco SD-WAN Controller, Cisco SD-WAN Validator, and Cisco vEdge Devices.
Discover the transformation of Cisco SD-WAN into Cisco Catalyst SD-WAN, simplifying networking solutions. Explore the benefits of this software-based approach and its impact on modern enterprise networks.