

2022/05/14 IT & Cyber-Security Solutions 1792 visit(s) 8 min to read
Ctelecoms

We have to admit, hackers are getting more and more creative by the second! And the numbers in cyber security reports are not very promising for regular users and enterprises alike.
The one thing that all these reports have in common is the fact that Emails are the most common attack surface there is worldwide!
So to avoid phishing attempts, bogus attachments, and compliance violations, we are here to recommend practices that will keep trouble at bay.
So without further ado, let’s jump right into the good stuff.
Well, it’s not just about having strong passwords and a limited contact list!
I mean it’s pretty easy to extract your email from data leaks since all of us are curious enough to through our emails everywhere.
Email security is a broad term that describes the many procedures and tactics for protecting both your email account and the content of each email you send and receive.
It’s also a critical part of your overall cybersecurity. Let’s be honest, you would say “I’m not sharing state secrets, so why would I care if my email got hacked?”
Well, hackers don’t just use email for the content, they can use your account as a gateway to reach a larger network. From there, they can jump from one thing to another, starting with confidential medical records to bank routing numbers to propriety information.
Here are the most common threat types that you should keep an eye on:

Phishing refers to any attack that asks for money or valuable information such as passwords, account numbers, and private information, and a spear-phishing attack is the one that uses your information to get it, it’s like impersonating you or a friend to take over another account or access private information.


Most hackers nowadays tend to depend on human error.
People are generally curious, that’s why this is considered a great opportunity for hackers to take over accounts and get their hands on valuable information.
Social engineering is defined as any kind of persuasion that causes people to click on a malicious email, link or attachment.
And it really works!
It’s considered a more specific type of spear-phishing, where hackers pretend to be the boss of a company or another high-level executive.
In this case, the scammer studies the habits of the employee to make the email appear much more believable!
This results in a fairly effective scam to steal anything from money to valuable information.
Spam emails are both annoying and dangerous! There are ways to include malicious links, malware, trojans, and other security threats in an innocent-looking advertisement.
Spam can be sent by real humans, but more often, it is sent by a botnet, which is a network of computers infected with malware and controlled by a single attacking party.
Email spam senders, or spammers, regularly alter their methods and messages to trick potential victims into downloading malware, sharing data or sending money.
It’s short for Malicious software and can refer to ransomware, trojans, or any software designed to attack your systems.
Ransomeware was designed to encrypt your files or your entire operating system so hackers can ask for cryptocurrency in exchange for restoring your files.
Of course, there’s no guarantee they are going to restore it, it’s just a chance you have to take.
On the other hand, trojans can give the hacker access or a backdoor to your entire system or machine, including your webcam!
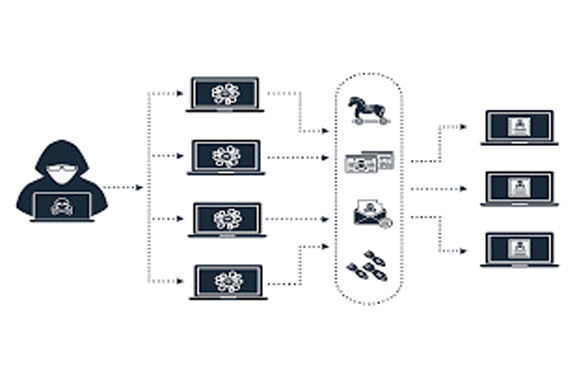
As we mentioned earlier, botnets are groups of devices controlled by hackers and used for widescale spam and phishing campaigns.
These can also be used to overload the systems, and this is known as Distributed Denial of Service attack or DDoS.
Now true email security really boils down to a mixture of human and technological prevention.
In short, you need to try and block these threats before they reach your mailbox so here are the best practices and solutions that can help you block these attacks.
This one is pretty simple!
Make sure to never download or view any attachment when you are not sure of the sender’s ID.
Even if you do know them, check with the sender to verify the message if you weren’t expecting an attachment.
Some people tend to turn off this filter to avoid missing important email messages as they are known to reach the wrong mail box.
However, this filter might not seem like much of a protection method, but it’s actually a great first line of defence against potential threats.
Most of the time you’ll get an alert that your password has been compromised or leaked, so all you have to do is not ignore it.
Make sure you have strong passwords and make the effort to change them every once in a while to avoid data leaking.
hackers have a way to intercept an email while it’s being routed between the sender and the recipient.
Encryption works as a way to scramble the original content of an email into an unreadable mess, with the true message only revealed with authentication from the recipient.
You can encrypt your emails through secure email hosting services or use a tool to secure both the content and the connection, such as Cisco Secure Email.
Cisco Email Security solution blocks threats so that companies receive only legitimate emails, so it would be a great addition to your team’s security measures.
Taking precautions to secure your emails is crucial to preventing email data loss, however, all these steps can really slow down your workflow.
To optimize email security, you can adopt data loss prevention systems DLP that manages all sensitive data in your network including your emails.
This system will identify and monitor any information that is in use or motion in real-time.
The 2FA protocol requires users to have a third piece of information on top of the basic username and password.
These systems are common in cloud-based email servers like Gmail, and they serve as an effective way to tighten the access points from end to end.
As a business owner, it’s always good to take your security measure to the next level. Data is really valuable, and hackers are working day and night to access what they can.
So, to help you get your hands on the best solutions that would make a difference for your email security here you can take a look at our solutions and choose the right one for your business: https://www.ctelecoms.com.sa/en/Solution11/IT---Cyber-Security-Solutions